100% Free Keylogger with Unlimited Keystroke Logging
100% Free Keylogger with Unlimited Keystroke Logging
Refog Free Keylogger is a 100% free Windows application with no trial limits and no time restrictions. It records every keystroke typed on the computer, tracks applications and websites, and captures chat conversations — with data accessible via a cloud dashboard. Download free.
Refog Free Keylogger is a truly free Windows application that records every keystroke typed on the computer. The keystroke logging feature works indefinitely with no time limits, no trials, and no requirement to pay or upgrade for basic keystroke recording.
DOWNLOAD FREE KEYLOGGER Instant Download | No Credit Card Required
Stop Settling for Limited "Free Trials"
Most so-called free keyloggers are actually trials that stop working or become limited after a few days. Refog Free Keylogger is different — the core keystroke recording feature works forever without any restrictions or payments.
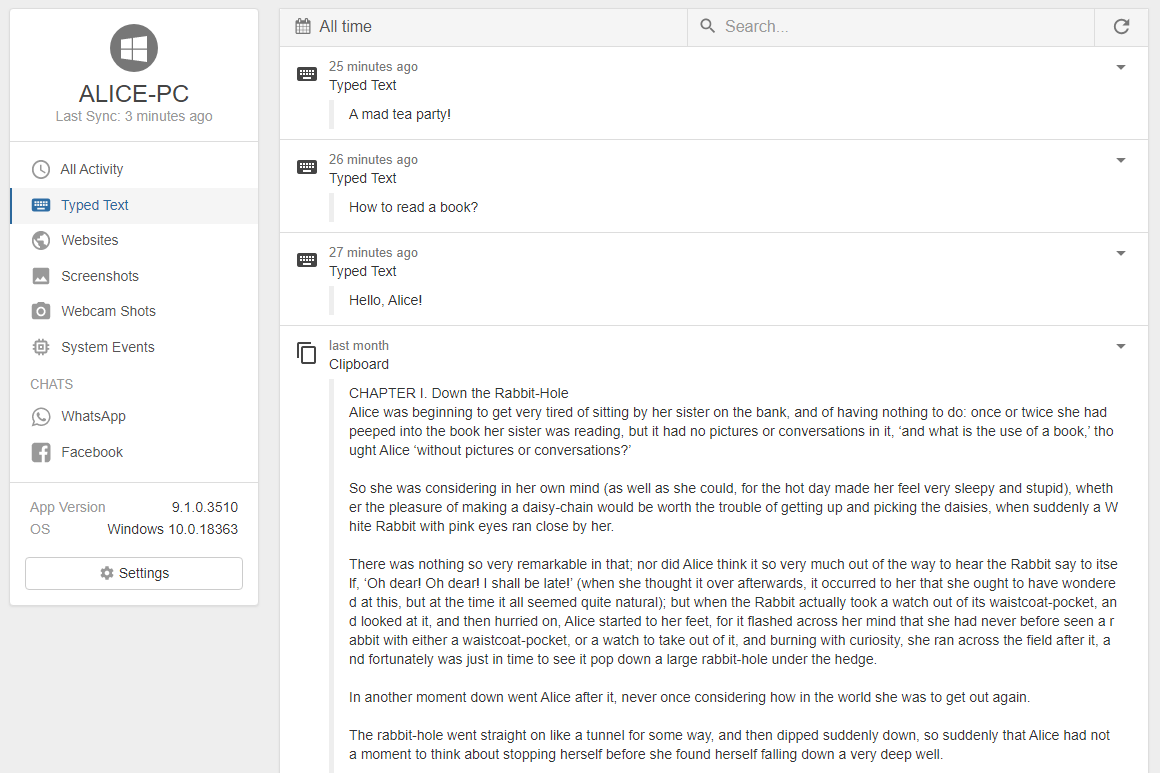
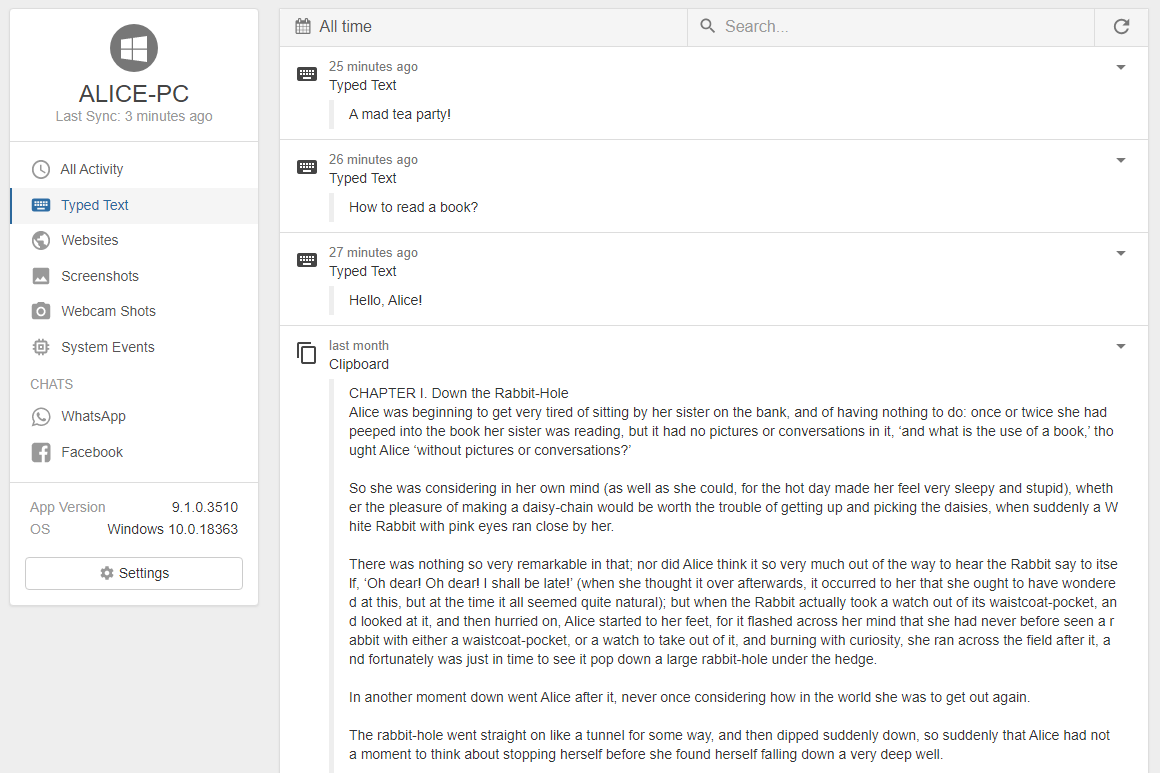
How It Works: Monitor in 3 Simple Steps
- Download & Install — Installation takes just a few minutes.
- Run Invisibly — The program works silently in the background and remains completely hidden.
- View Logs — Access and review all recorded keystrokes directly on the computer anytime.
What You Can Monitor with Refog Free Keylogger
Unlimited Keystroke Recording
Captures every single key pressed in any application — web browsers, messengers, email, documents, games, and more. Every entry is timestamped and shows which program was active at the time.
Trusted by Parents and Individuals
"I was looking for a simple way to know what my kids were doing online. Refog Free Keylogger was the perfect solution. It's easy, it works, and it's actually free."
— Mark D., Parent
"Refog's free tool does exactly what it promises: logs every key without any fuss or cost. It gives me great peace of mind."
— Jennifer L.
Frequently Asked Questions
▼
Is Refog Free Keylogger actually free?
Yes — and not in the "free trial" sense. The core keystroke logging feature has no time limit, no feature cap, and no credit card requirement. Most tools that call themselves free disable key functionality or stop working after 3–7 days to push you toward a paid plan. Refog's free version has worked the same way for over two decades: download it, install it, and it records keystrokes indefinitely without ever asking you to upgrade.
►
What does it record?
Every keystroke typed in any application on the PC — browsers like Chrome, Edge, and Firefox, messaging apps, email clients, document editors, games, and anything else. Each entry in the log is timestamped and tagged with the application where the input occurred, giving you a clear, chronological record of all typed activity.
►
Will the person using the computer know it's installed?
No. Once installed, the software does not appear in the taskbar, the system tray, or the list of programs in Windows Settings. It is not visible in Task Manager under any recognizable name. The program runs silently in the background and can only be accessed by the person who set it up, using a password configured during installation.
►
Which versions of Windows does it support?
Refog Free Keylogger is fully compatible with Windows 10 and Windows 11, including all major feature updates to both. It runs on 32-bit and 64-bit systems without requiring additional drivers or software. The installer is lightweight and has a minimal system footprint, so it does not affect the performance of the monitored PC.
►
How do I install it?
Download the installer from the official Refog website and run it on the target computer. The setup wizard walks you through the process in a few minutes — you choose whether to run in stealth mode and set a password to protect access to the logs. No technical background is needed. The entire process is designed to be straightforward for any PC user.
►
What does the paid version add?
The free version is dedicated to unlimited keystroke logging and works indefinitely without any restrictions or payments. Paid plans significantly expand the monitoring by adding website visit history, periodic screenshot capture, activity tracking in messaging apps such as WhatsApp, Telegram, and Facebook Messenger, and remote log delivery by email. If knowing what is typed on the PC is your primary goal, the free version is completely sufficient. The paid upgrade is for those who want a fuller view of computer activity.
►
Is it legal to use a keylogger?
It depends on context and jurisdiction. Installing monitoring software on a computer you own — such as a family PC to oversee a child's activity, or a company device with employees' informed consent — is generally lawful in most countries. Installing it on someone else's computer without their knowledge for the purpose of accessing personal data, passwords, or financial information is illegal. Refog Free Keylogger is built for transparent, consent-based use. If you are unsure whether your specific situation is covered, consult a legal professional familiar with the laws in your country or state.
Ready to Start Monitoring?
Download the 100% free keylogger now. Keystroke logging works indefinitely.
 100% Free Keylogger with Unlimited Keystroke Logging
100% Free Keylogger with Unlimited Keystroke Logging